Whenever we login to our AWS(Amazon Web Services) account a default VPC is created with the CIDR (172.31.0.0/16). VPC stands for Virtual Private Cloud, it is virtual private network and is isolated from other virtual networks in your AWS account, we can launch EC2, RDS and Elastic Cache instances using our own created VPC.
In this article we will demonstrate how to setup our own VPC in your AWS account. Let’s assume I want to launch two ec2 instances one will used for application server and it will be accessed over the Internet and second instance will be used for Database server. My application instance will connect to Database instance internally using VPC subnet and also don’t want to allow DB instance to be accessed over internet.
Refer beneath steps to setup VPC and launch EC2 instances using your VPC
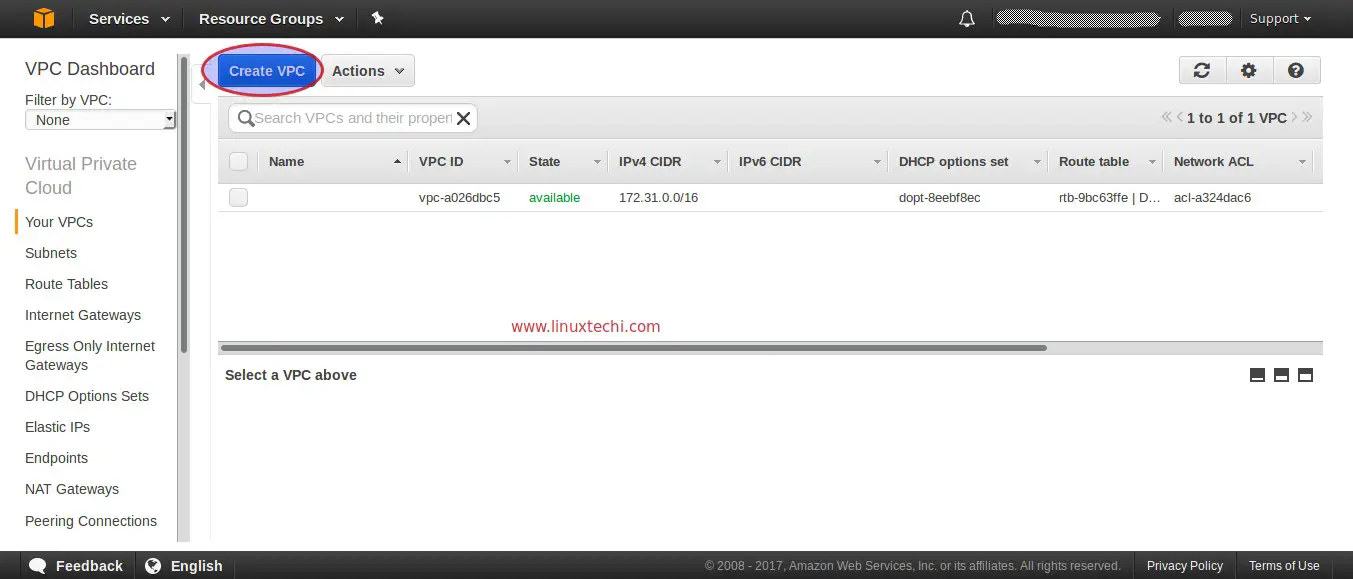
Step1: Create your VPC
Login to your AWS account, From the Services Tab → Select VPC →then Select Your VPC → click on “Create VPC”
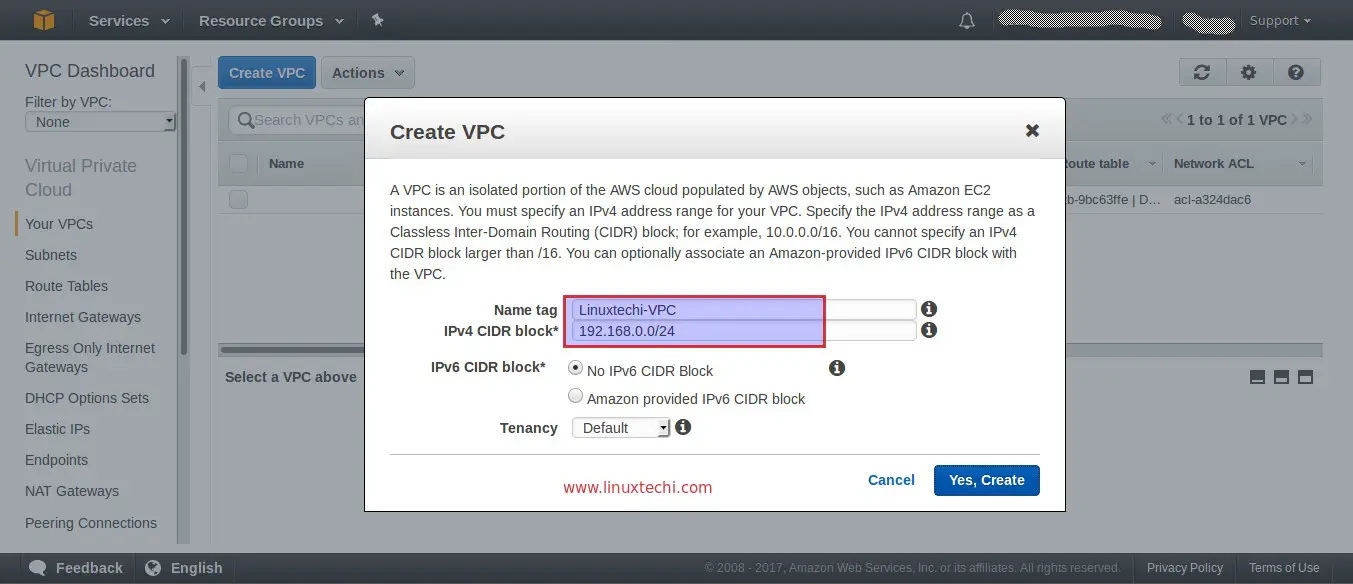
Specify your VPC Name and CIDR (Classless Inter-Domain Routing), In my case I am using the followings
- VPC Name = Linuxtechi-VPC
- IPV4 CIDR = 192.168.0.0/24
Click on “Yes,Create” option
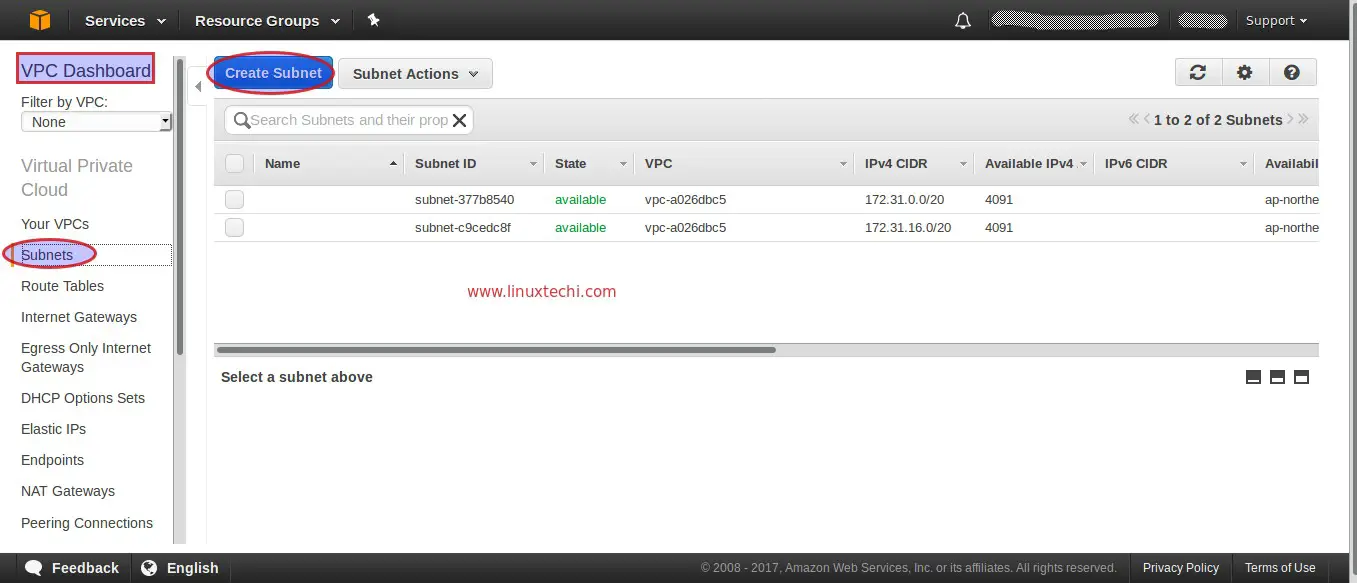
Step:2 Create Private Subnets
In this step we will create two private subnets, Subnet1 (192.168.0.0/25) and Subnet2 (192.168.0.128/25) across the availability zones. We are calling these subnets as private because we can’t access instances from the Internet whenever EC2 instance is getting IP from these subnets. Though after attaching Internet gateway these instances becomes reachable over internet.
From the VPC Dashboard click on Subnets option and then click on Create Subnet
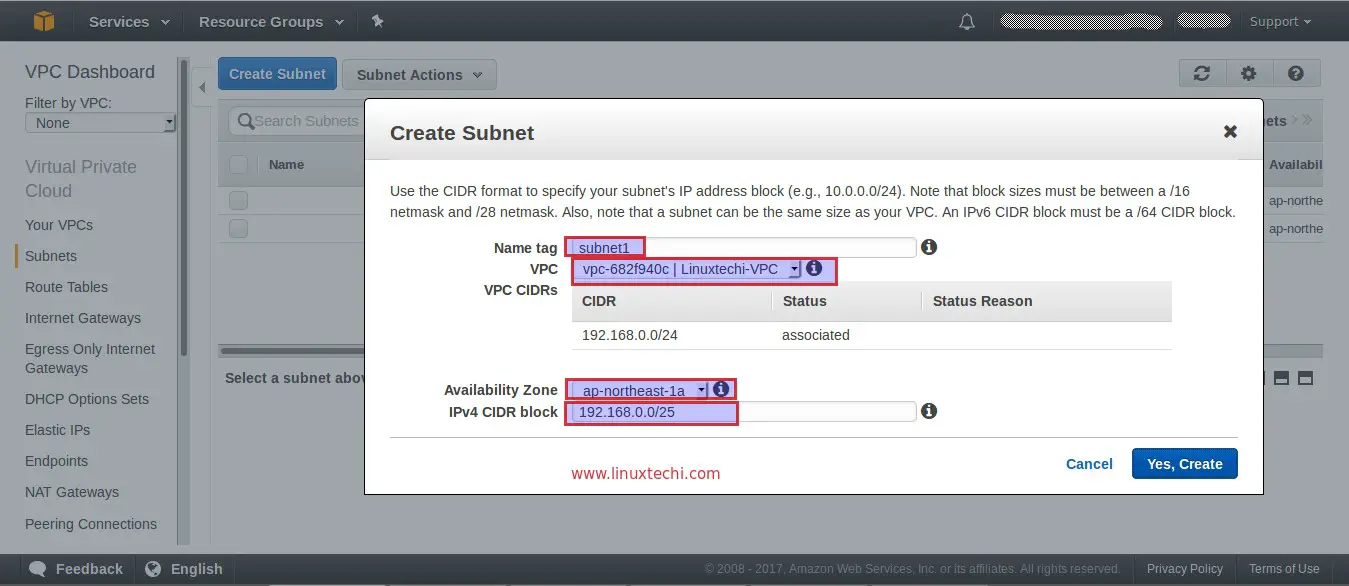
Specify the followings
- Subnet name as “subnet1”
- VPC ( Linuxtechi-VPC)
- Availability zone as per your region
- IPV4 CIDR “192.168.0.0/25”
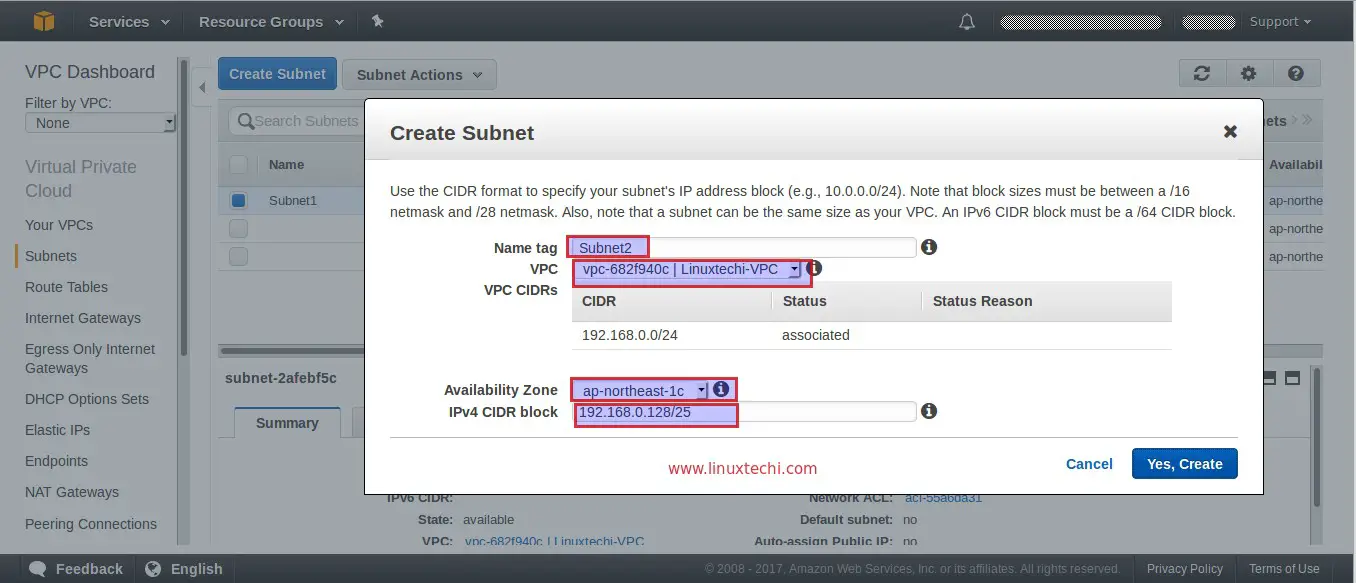
click on “Yes, Create”, Similarly Create Subnet2 with IPV4 CIDR “192.168.0.128/25”
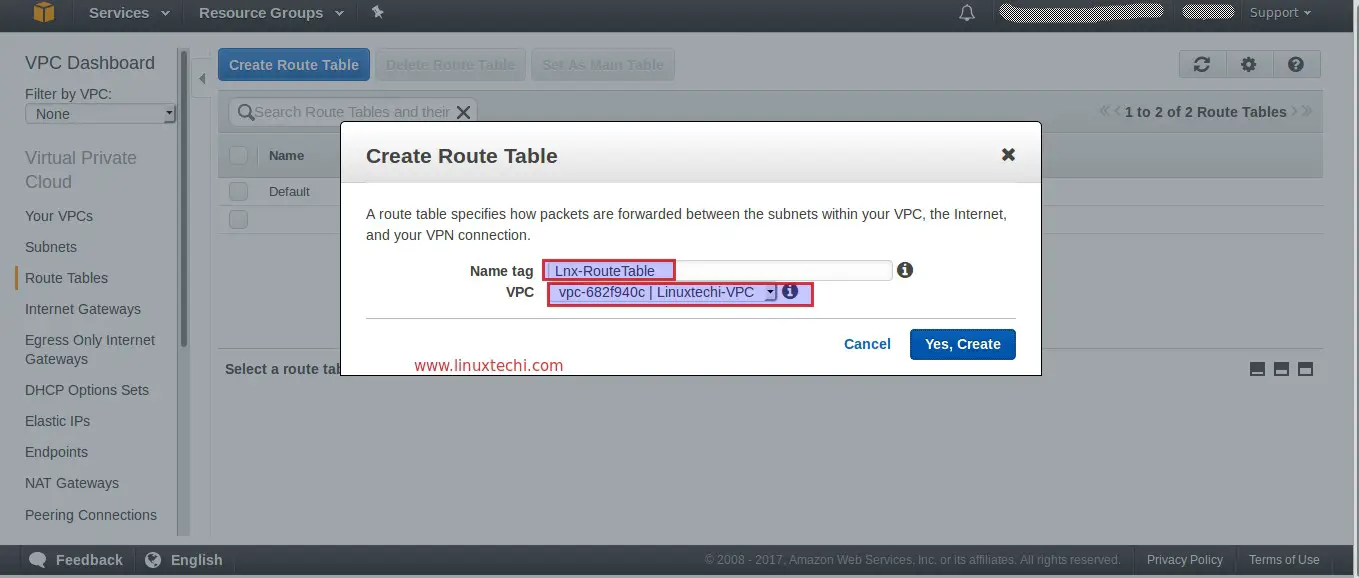
Step:3 Create a Route table and associate it with your VPC
From VPC Dashboard there is an option create a Route table. Click on “Create Route Table”
Specify the Name of Route Table and Select your VPC, In my case VPC is Linuxtechi-VPC
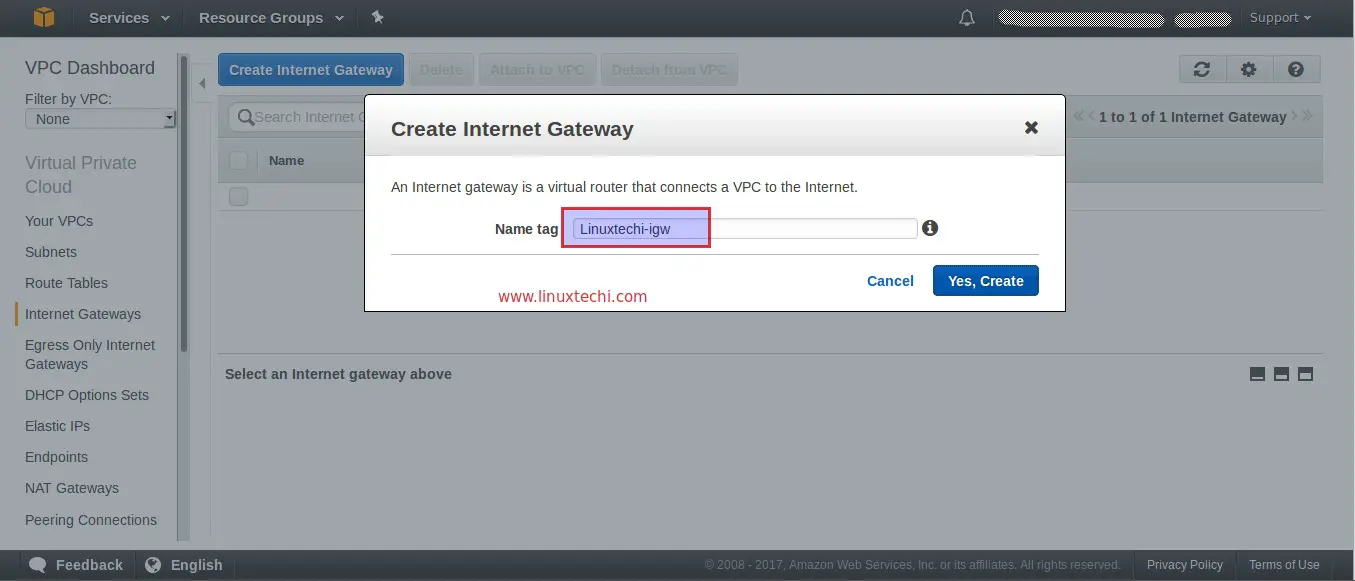
Step:4 Create Internet Gateway (igw) and attached it to your VPC
From VPC dashboard there is an option to create Internet gateway. Specify the Name of Internet gateway
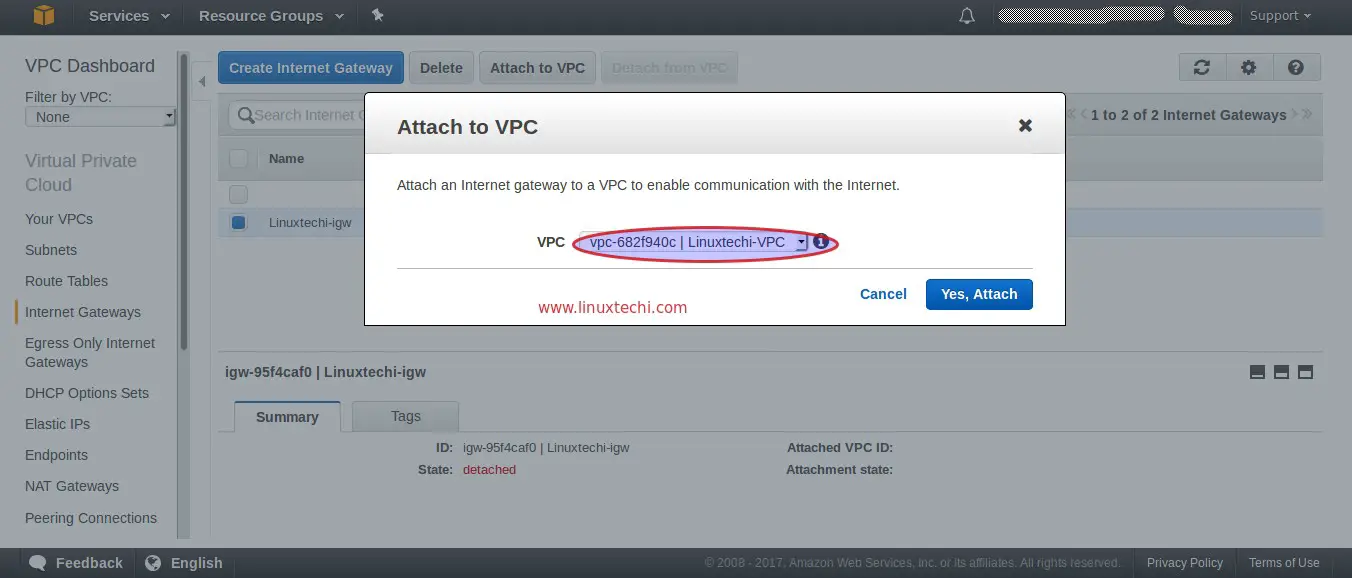
Once the Internet gateway is created, attached it to your VPC, Select and Right Click Your Internet gateway and then Select the “Attach to VPC” option
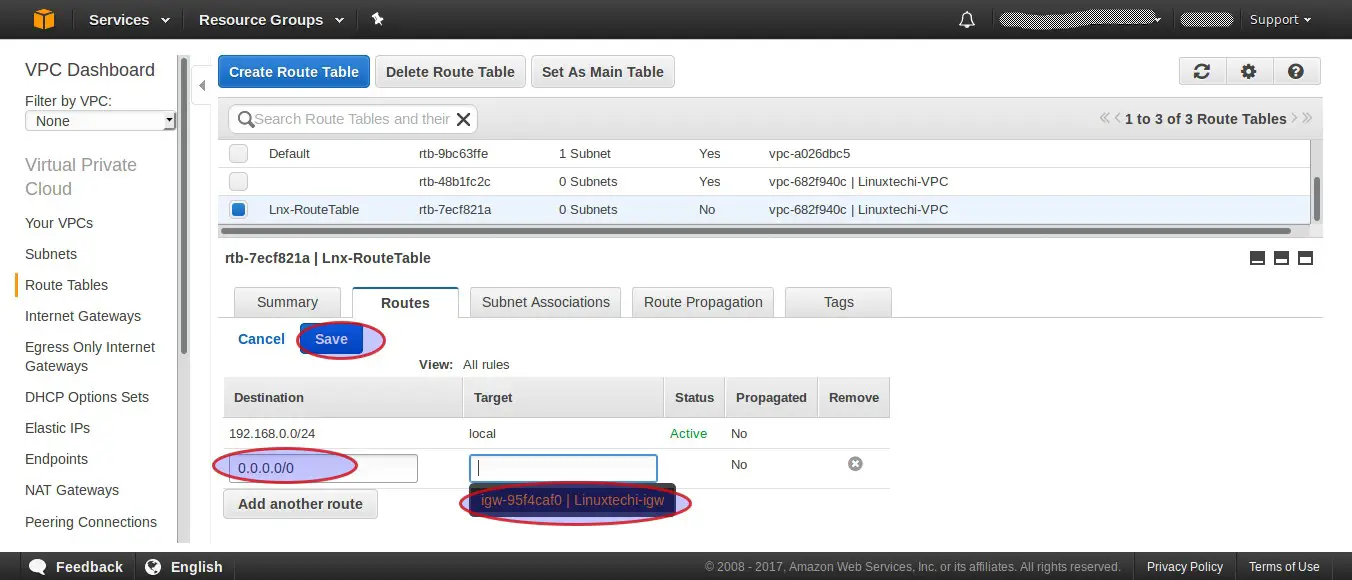
Now Add Route to your route Table for Internet, go to Route Tables Option, Select your Route Table, In my case it is “Lnx-RouteTable“, click on Route Tab and Click on Edit and the click on “add another route”
Mention Destination IP of Internet as “0.0.0.0/0” and in the target option your Internet gateway will be populated automatically as shown below.
Click on Save
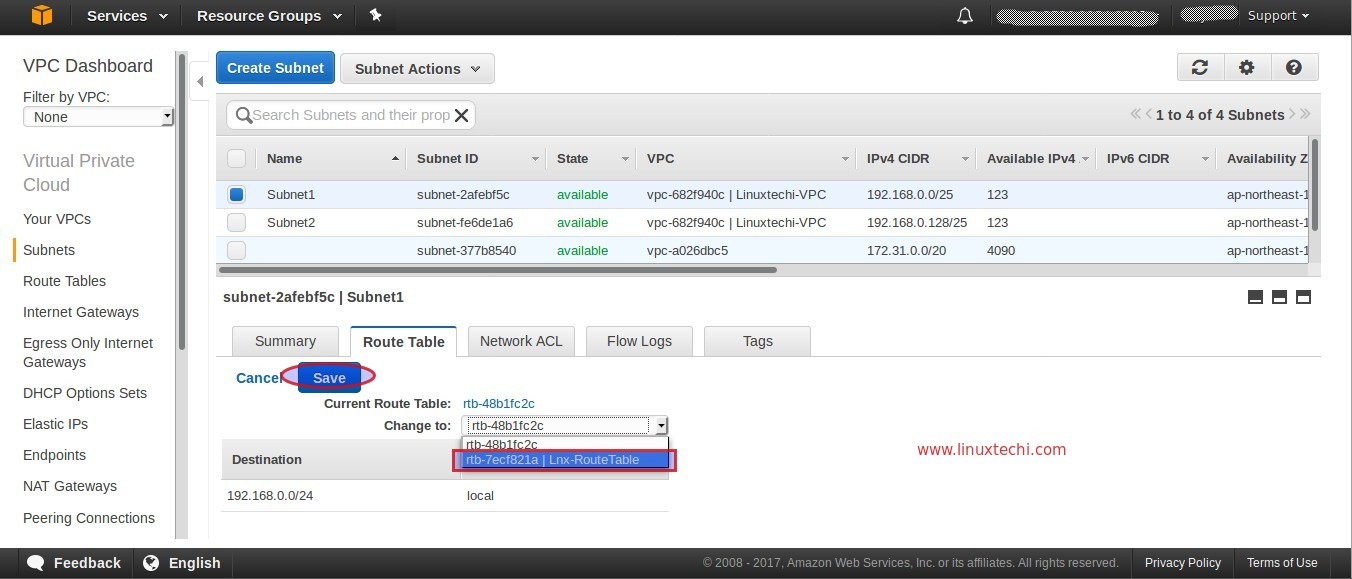
Step:5 Change Route table of your VPC Subnet
In above steps we have created two Subnets (Subnet1 and Subnet2), I am going to change the route table of Subnet1.From the VPC Dashboard, Click on Subnets, Select the Subnet1 and the click on “Route Table” Tab and the click on Edit.
Change the default Route table to “Lnx-RouteTable” and then Click On Save
Now onwards whenever an EC2 instance is launched in your VPC using Subnet1 then we can access that instance from Internet and Instance launched using subnet2 will not accessible over Internet but it will be accessible internally.
Step:6 Launch APP and DB Server Instance in your VPC
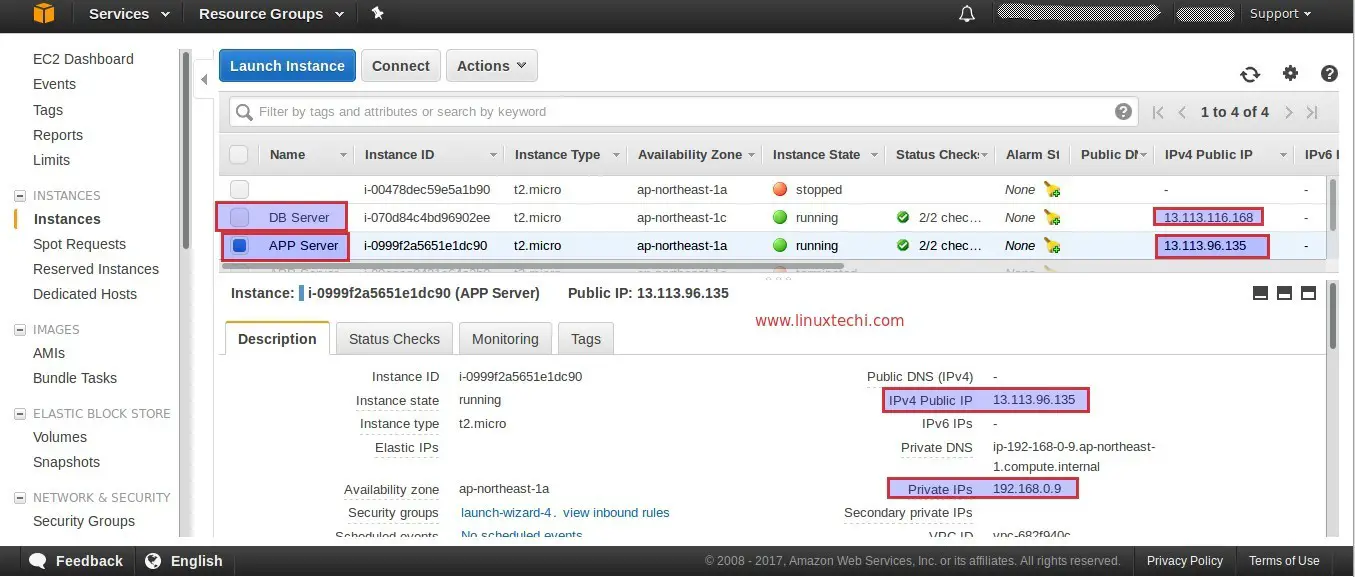
Launch APP Server in your VPC using Subnet1 and DB Server using Subnet2. Verify whether you are able to access APP Server and DB server from public IP.
Try to SSH APP Server with its Public IP
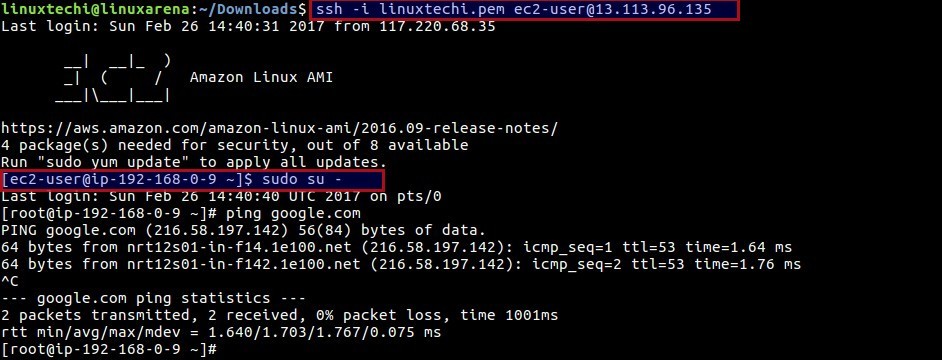
Try SSH DB Server with its Public IP
linuxtechi@linuxarena:~/Downloads$ ping 13.113.116.168 PING 13.113.116.168 (13.113.116.168) 56(84) bytes of data. ^C --- 13.113.116.168 ping statistics --- 8 packets transmitted, 0 received, 100% packet loss, time 7056ms linuxtechi@linuxarena:~/Downloads$ ssh -i linuxtechi.pem [email protected] ssh: connect to host 13.113.116.168 port 22: Connection timed out linuxtechi@linuxarena:~/Downloads$
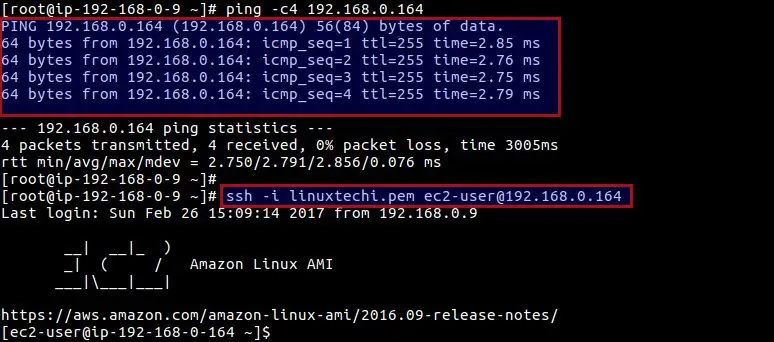
We can’t access the DB server from Internet because it is launched with Subnet2 with its default Route table and Internet gateway is not associated to route table of Subnet2. Though we can access the DB Server from APP server with its private IP.
That’s all for this article and hope you guys got an idea how setup your own VPC in your AWS account. Please don’t hesitate to share your feedback and comments 🙂
Also Read : How to Create and Add EBS Volume in AWS Instance
Also Read: How to Extend EBS Boot Disk of EC2 Instance without Reboot
with the help of your article I am able to configure my own vpc thank you for detail information about this.
Awesome VPC Tutorial
Better than Amazon
DO we need to make lnx-Route table as Main table.
my instance not launching if it is not main route table.
amazon tutorials are crap. they just play hard to get for KISS. this is the best intro.
Iam have not satisfied in understanding the concepts of VPC for more than 1 month since i started to learn AWS. Finally i came across your tutorials and really impressed and understood the concepts clearly through real time scenario .
Thanks a lot . Your work towards the sharing the knowledge is awesome and must be appreciated ..
Well done . You did a great job !
Excellent tutorial. To the point with clarity. Keep up the good work.