Ansible is a fantastic automation and orchestration tool popular among many developers owing to its simplicity and ease of use. One of the most important features that comes with Ansible is the Ansible Vault. As you would guess it by now, Ansible vault is a security feature that is used for encrypting or securing sensitive information in playbooks or files instead of having them in plain text which would pose a significant threat in the event of a breach. Such data includes passwords, API tokens and SSL certificates to mention a few. You can encrypt entire playbook YAML files of a string within the playbook with sensitive information such as a password.
In this guide, we look at various ways that Ansible vault can help you lock down your sensitive or confidential information and keep snoopers at bay.
Create an Encrypted File using Ansible Vault
Ansible vault uses the ansible-vault command line utility tool for encrypting sensitive information using the AES256 algorithm. This provides symmetric encryption which is embedded to a defined password. A user can use the same password to either encrypt or decrypt files in order to access content.
To create an encrypted file, use the ansible-vault utility tool as shown
$ ansible-vault create file.yml
For example, to create a file, call it secret_file.yml, run the command
$ ansible-vault create secret_file.yml
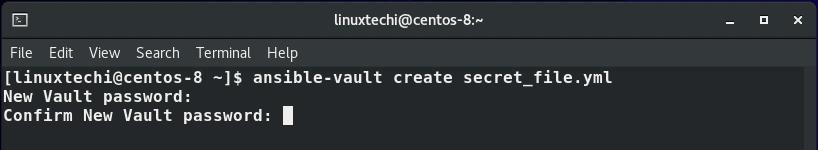
You will be prompted to provide a new vault password. Key in your preferred password and confirm. Once you have confirmed the password , vim editor will be launched.
Thereafter, type the file content that you wish to be encrypted by Ansible vault and save the file. Below is some sample text.
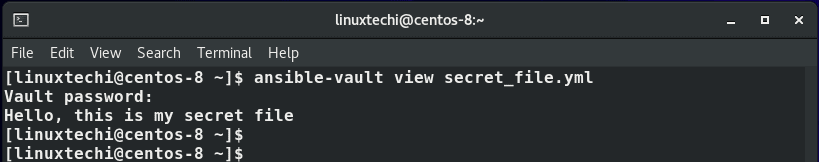
Hello, this is my secret file
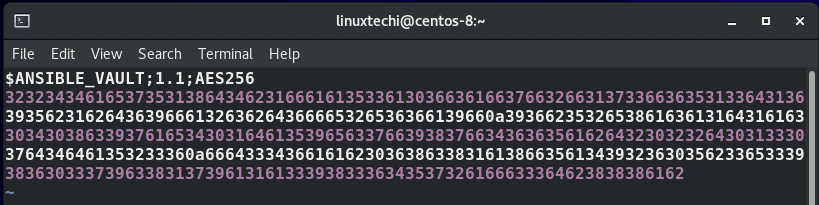
When you view the file, you will discover that it has already been encrypted using AES256 algorithm as shown.
$ vim secret_file.yml
Edit an Encrypted File with Ansible Vault
To make changes to an already existing file which is encrypted use the syntax:
$ ansible-vault edit file.yml
From our sample file that we created earlier on, the command for editing the file would be:
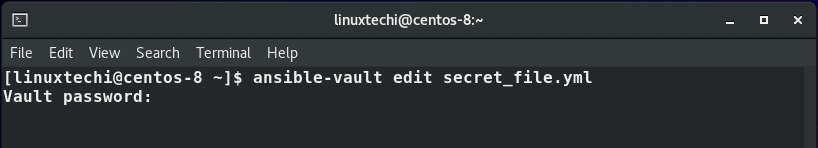
$ ansible-vault edit secret_file.yml
Again, you will be prompted for the vault password, and after providing it, you will be granted access to the file to make modifications.
View an Encrypted File
To have a peek at an encrypted file, use the syntax:
$ ansible-vault view file.yml
Using our file, the command will therefore be
$ ansible-vault view secret_file.yml
Encrypt an Existing File using Ansible Vault
Suppose you want to encrypt an already existing file which is unencrypted, say an inventory file. How would you go about it? To achieve this, use the syntax:
$ ansible-vault encrypt file.yml
For example, to encrypt a file file1.yml execute the command:
$ ansible-vault encrypt file1.yml
Specify the vault password and confirm it to encrypt the file.
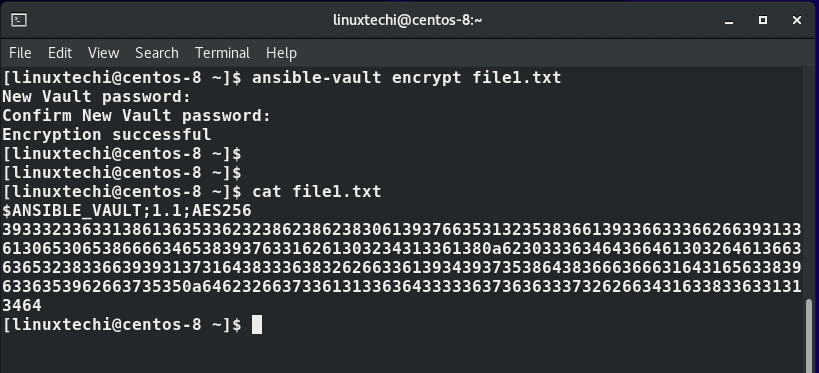
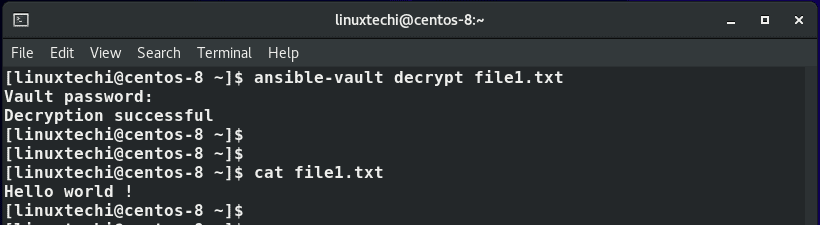
Decrypt a File using Ansible Vault
To decrypt a file and revert to plain text, run the command:
$ ansible-vault decrypt file1.yml
If all went well, you will get a ‘Decryption successful’ message. You can now use the cat command to view the contents of the file.
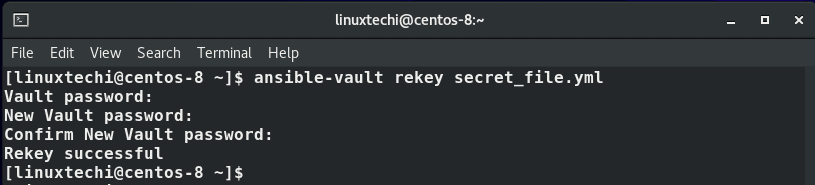
Reset Ansible vault Password
Also, you can reset or change the Vault’s password. This is done using the rekey option in the ansible vault command as shown:
$ ansible-vault rekey secret_file.yml
Specify the current vault password first , and later create a new password and confirm it.
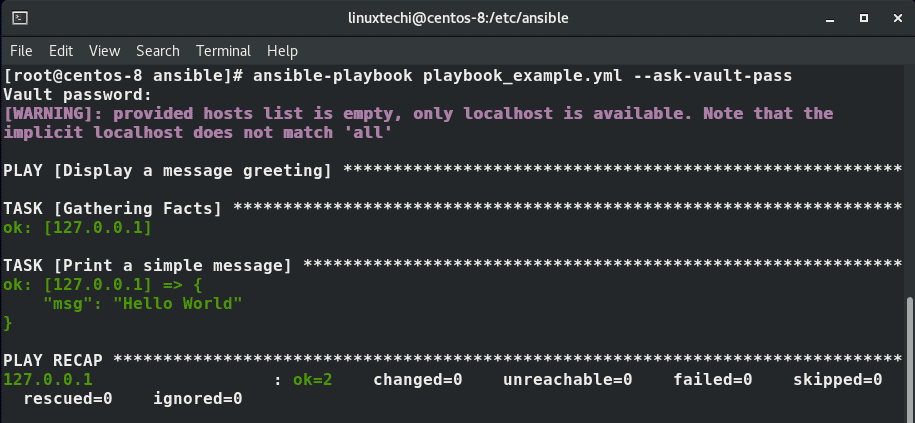
Decrypting Content at Run Time in Ansible Playbook
Prior to Ansible 2.4, decrypting files during run time required the use of the –ask-vault-pass parameter as shown with either ansible or ansible-playbook commands:
$ ansible-playbook playbook_example.yml --ask-vault-pass
You would then be prompted for a Vault password and the decryption will begin at runtime.
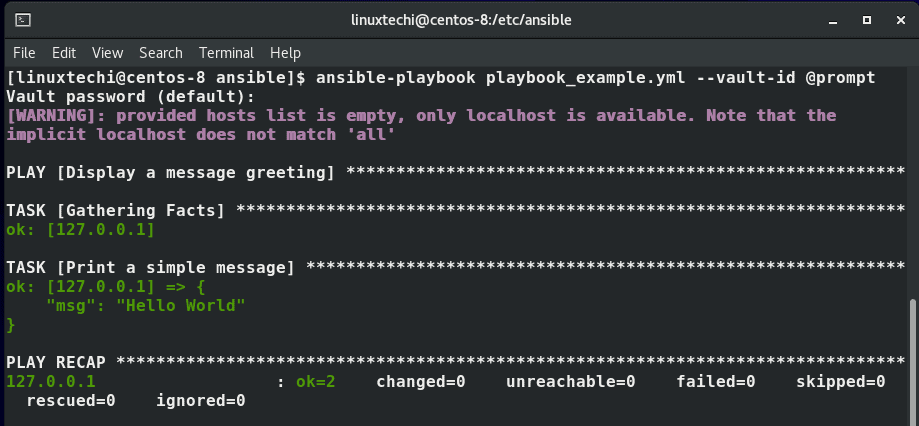
However, that has been deprecated. Since Ansible 2.4 the standard method of prompting for a password is to utilize the –vault-id option as shown.
$ ansible-playbook playbook_example.yml --vault-id @prompt
The @prompt will prompt for the password
A simple trick to avoid being prompted for a password every time you are decrypting files during runtime is to store the vault password in a file.
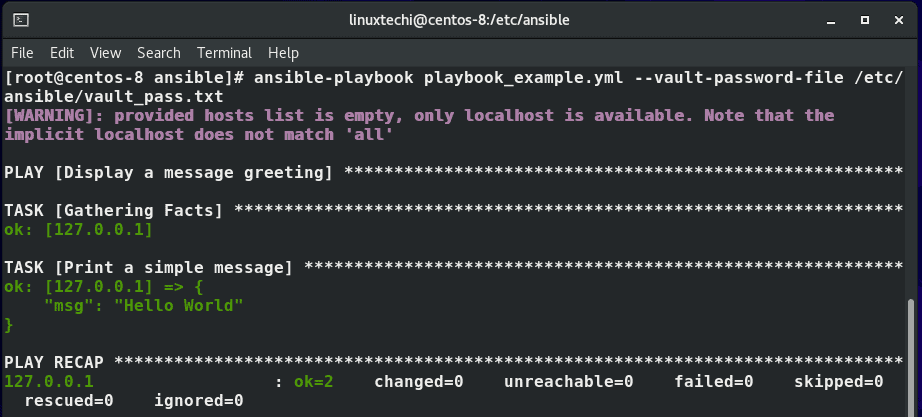
Prior to Ansible 2.4 the way to achieve this was the use of the –vault-password-file parameter to specify the path to the file that contains the stored password.
For example, in the demonstration below, the password file is located in the /etc/ansible/vault_pass.txt file.
$ ansible-playbook playbook_example.yml --vault-password-file /etc/ansible/vault_pass.txt
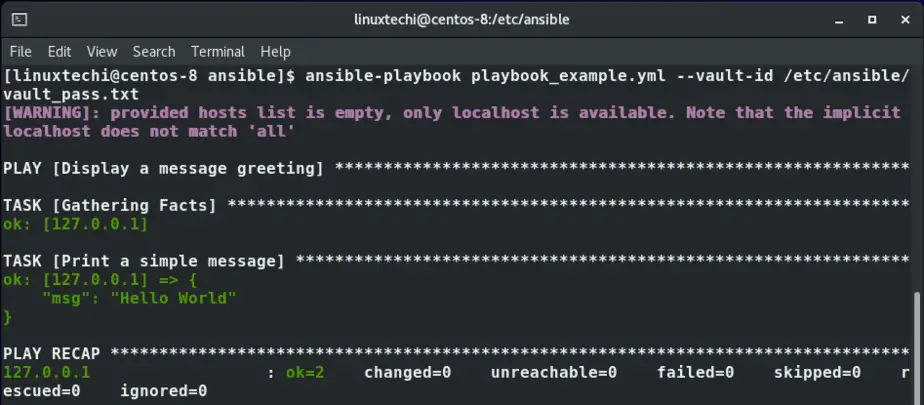
However, just like the –ask-vault-pass option, the option –vault-password-file has been deprecated to pave the way for the –vault-id option. The command, therefore, looks like this:
$ ansible-playbook playbook_example.yml --vault-id /etc/ansible/vault_pass.txt
Encrypting a variable in Ansible Playbook
Apart from encrypting an entire playbook, ansible-vault also gives you the ability to encrypt variables only. In most cases these are variables bearing highly confidential & sensitive information such as passwords and API keys.
The playbook below is intended to print out the value of the variable my_secret which contains a password defined as P@ssword123.
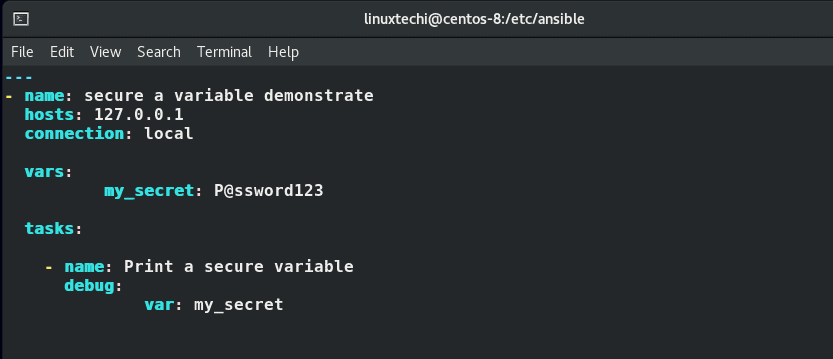
Generally, it’s a bad idea to store passwords in plain text because if anybody gets a hold of the playbook file, your security can be compromised.
You are therefore presented with 2 options: to encrypt the entire file or encrypt the value of the variable.
To encrypt a variable, use the encrypt_string option as shown.
$ ansible-vault encrypt_string ‘string’ –name ‘variable_name’
To encrypt the value of the variable my_secret on the playbook example, the command will be:
$ ansible-vault encrypt_string 'P@ssword123' --name 'my_secret'
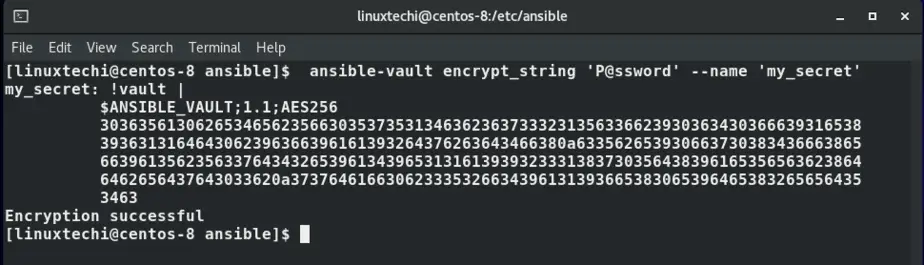
The output above indicates that the password has been encrypted with AES 256 encryption. From here, copy the entire encrypted code from !vault | . Head out to the playbook file and delete the plaintext password value and paste the encrypted value as shown.
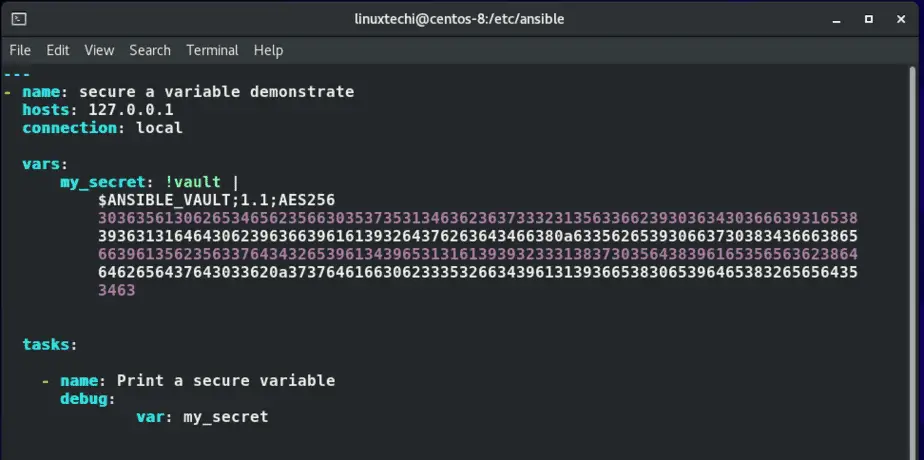
Save and exit the file. Now run the playbook and verify whether it will still display the value of the password stored in the my_secret variable.
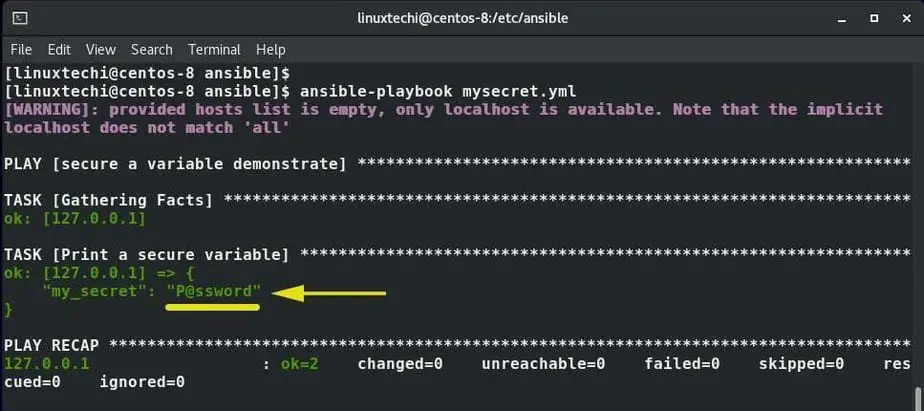
The output above shows that the playbook gives the desired results implying that we succeeded in encrypting the variable.
This wraps up this tutorial on Ansible Vault. You can now secure your files and keep your confidential information away from prying eyes.
Read Also : How to Use Jinja2 Template in Ansible Playbook
I use and love Linux, but am a GUI guy. Maybe my data is not that sensitive, but I use Engrampa Archive Manager and 7zip. It compresses the files, password protects it and gives me the option to hide the file names or not. That works well for me. I doubt I have the skills to use Ansible Vault, starting with my typing ability. If you are not a terminal whiz, it works well.
@Jim – Ansible Vault is a tool for encrypting yaml and sensitive files in conjunction with Ansible. If you aren’t using Ansible, this article won’t apply to you at all. It is not really a user space tool for encrypting files on a daily basis.