In this blog post, we will cover how to lock and unlock user account after failed SSH logins in Linux.
In today’s interconnected world, the security of our systems is of utmost importance. One crucial aspect of securing a Linux system is protecting it against unauthorized access through SSH.For production servers. It is recommended that one should enable ssh policy, means user’s account should be locked automatically after n numbers of failed ssh login attempts.
Lock User Account After Failed SSH logins in RHEL / Rocky Linux / AlmaLinux
In Linux distribution like RHEL, Rocky Linux, AlmaLinux, CentOS and Fedora, this is achieved by using pam module “pam_faillock” and for Debian like distributions, this can be achieved using “pam_tally2” pam module.
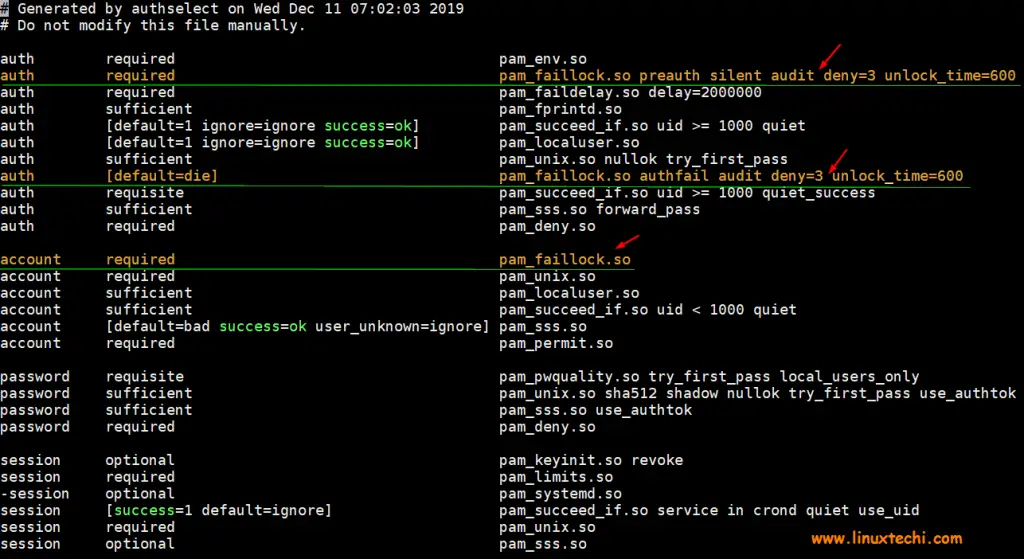
Add the following lines in auth section in these two files using vi editor.
- /etc/pam.d/password-auth
- /etc/pam.d/system-auth,
auth required pam_faillock.so preauth silent audit deny=3 unlock_time=600 auth [default=die] pam_faillock.so authfail audit deny=3 unlock_time=600 account required pam_faillock.so
Where,
- Audit –> it will enable audit logs for user login attempt in secure log file
- Deny=3 –> it will lock the user after 3 unsuccessful login attempts, you can change this number as per your requirement
- unlock_time=600 –> it means user’s account will remain locked for 10 minutes (600 seconds), if you want user account to be locked forever then set this parameter as “unlock_time=never“
Note: To lock root account as well after n incorrect logins, add “even_deny_root” parameter in auth section lines, example is shown below
auth required pam_faillock.so preauth silent audit even_deny_root deny=3 unlock_time=600 auth [default=die] pam_faillock.so authfail audit even_deny_root deny=3 unlock_time=600
As we can see above, we have two lines for auth section and one line for account section, order is very important while adding these lines to the files. Example is demonstrated below where these lines needs to be added,
$ sudo vi /etc/pam.d/password-auth
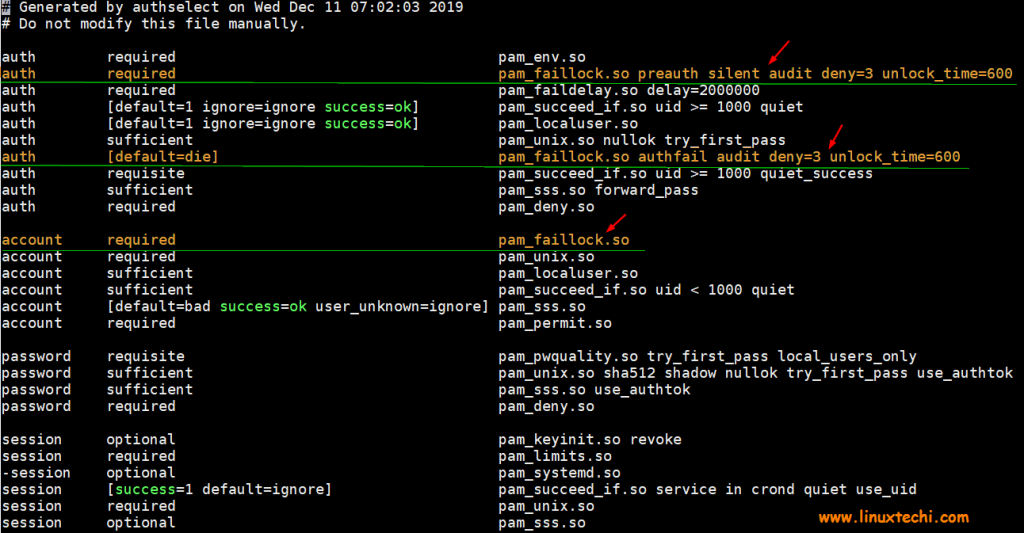
$ sudo vi /etc/pam.d/system-auth
After making changes in both the files, restart the ssh service to make above changes into the effect.
$ sudo systemctl restart sshd
Let’s do the testing whether user account will be locked after three unsuccessful login attempts or not.
Let’s assume we have a local account with name “pkumar“, we will try to ssh our Linux system with this account with incorrect passwords,
$ ssh [email protected] [email protected]'s password: [email protected]'s password: [email protected]'s password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password).
Now view secure logs using tail command,
# tail /var/log/secure
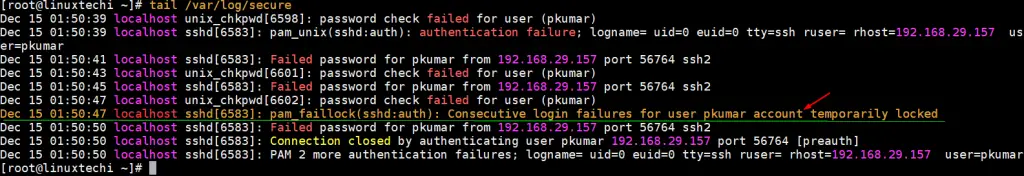
Above logs confirms that account has been locked after three incorrect login attempts, let’s verify from faillock command as well,
[root@linuxtechi ~]# faillock --user pkumar pkumar: When Type Source Valid 2019-12-15 01:50:39 RHOST 192.168.29.157 V 2019-12-15 01:50:43 RHOST 192.168.29.157 V 2019-12-15 01:50:47 RHOST 192.168.29.157 V [root@linuxtechi ~]#
Unlock User Account After Failed Logins in RHEL / Rocky Linux / AlmaLinux
To flush or clear these unsuccessful login attempts, execute the following faillock command,
$ sudo faillock --user pkumar --reset $ sudo faillock --user pkumar pkumar: When Type Source Valid $
Let’s move to Debian like distribution (Ubuntu, Linux Mint and Debian)
Lock User Accounts After Failed SSH Logins in Debian / Ubuntu / Linux Mint
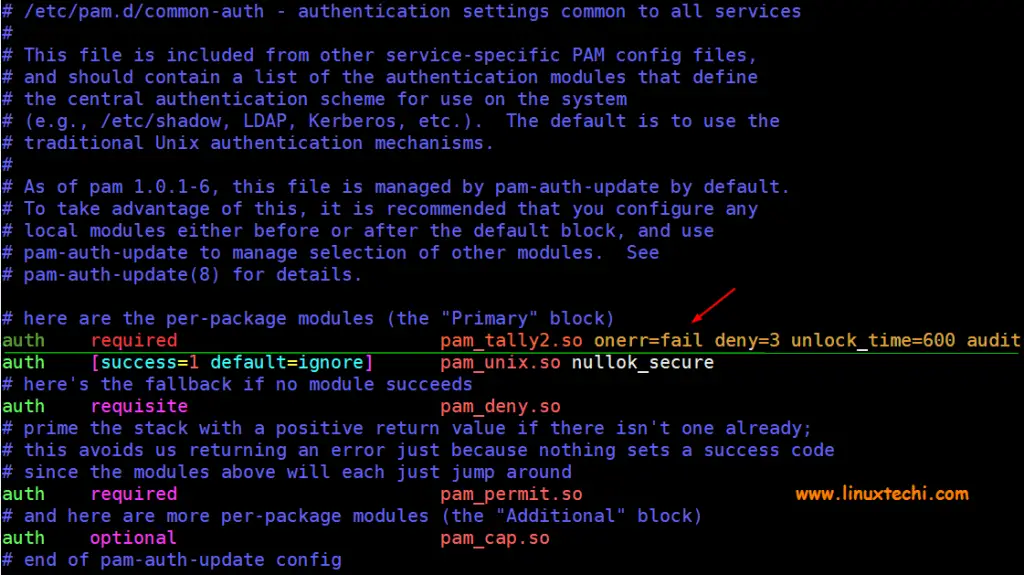
In order to lock user accounts after failed ssh login attempts in Debian, Ubuntu & Linux Mint, add the following line in the file “/etc/pam.d/common-auth“.
auth required pam_tally2.so onerr=fail deny=3 unlock_time=600 audit
if you wish to lock root account as well after three incorrect logins then add the following line ,
auth required pam_tally2.so onerr=fail deny=3 unlock_time=600 audit even_deny_root root_unlock_time=600
Where:
- Onerr=fail –> In case of error issue a fail
- deny=3 –> After three unsuccessful login attempts account will be locked
- unlock_time=600 –> It means account will remain locked for 10 minutes or 600 seconds
- audit –> It means audit the logs in audit.log file
- even_deny_root –> Lock the root account after three incorrect logins
- root_unlock_time=600 –> Root account will remain locked for 10 minutes or 600 seconds after 3 unsuccessful login attempts
Let’s add above discussed line in file “/etc/pam.d/common-auth” using vi editor,
$ sudo vi /etc/pam.d/common-auth
After making the above changes, save and exit the file and restart ssh service using following command,
$ sudo systemctl restart sshd
Let’s test whether accounts are locked after 3 incorrect ssh login attempts.
Assume we have a local user “devops“, we will try to ssh Ubuntu system with incorrect passwords
$ ssh [email protected] [email protected]'s password: [email protected]'s password: d [email protected]'s password: Permission denied (publickey,password).
Now view auth log file to see whether incorrect login attempts are captured or not,
$ tail /var/log/auth.log
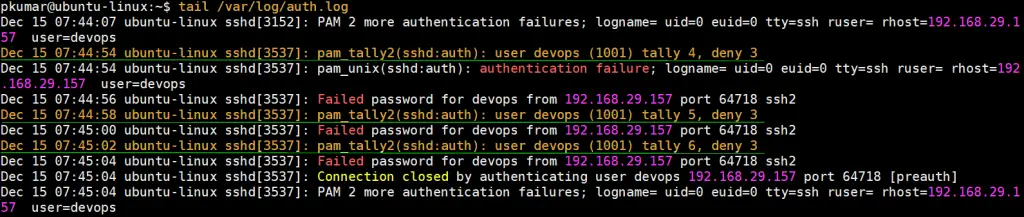
Above logs confirms that account has been locked, let’s verify from pam_tally2 command,
$ sudo pam_tally2 -u devops Login Failures Latest failure From devops 6 12/15/19 07:45:02 192.168.29.157 $
Unlock User Account using pam_tally2 command in Debian / Ubuntu / Linux Mint
In Debian like distributions, pam_tally2 command is used to unlock the user account. So, to clear these unsuccessful login attempts for devops user run following pam_tally2 command.
$ sudo pam_tally2 -u devops --reset Login Failures Latest failure From devops 6 12/15/19 07:45:02 192.168.29.157 $ $ sudo pam_tally2 -u devops Login Failures Latest failure From devops 0 $
That’s all from from this post, I hope you have found it useful and informative. Please don’t hesitate to post your queries and feedback in below comments section.
Read Also : How to Enforce Password Policies in Linux (Ubuntu / RHEL)
Very clear explanation. Thank you!
do you know how can i set max login limits for a specific group in linux?
Thank you Pradeep, great article, but I believe “even_deny_root root_unlock_time=600” is not a new line but the continuation of the previous (additional parameters). Maybe that’s what you meant, but it is not very clear.
Hi Oriol,
It would be in the same line. By doing so , we are implementing the same rule even for root user.
It is better to disable password login all together in ssh, use key based login instead
it’s not working for 1hour
Can you also please update for Ubuntu 22.04 LTS
i am using rhel 8.8.
i am able to get users locked out after 3 unsuccessful login attempts using “su – kav”.
but ssh is not getting user locked out.
ssh [email protected]I am using AuthSelect to manage system-auth/password-auth. Also using corresponding files in /etc/security/pwquality.conf + pwhistory + faillock.conf.